ACES3301 CTF
---
Last March 2025, the Alliance of Computer Engineering Students (ACES) from the Polytechnic University of the Philippines, held its annual Computer Engineering week, filled with seminars from respected professionals, academic and non-academic competitions as well as a party celebration.
ACES also added new competitions into play including its first ever Capture-the-Flag competition, facilitated and authored by non other than me!:) The participants were Computer Engineering students, with 1 team representative per year. As per request, the challenges were not difficult, but rather designed to teach and provided a fun and interactive learning experience in Cybersecurity.
Without further words, let’s tackle the challenges by category!
### Easy
#### **Bad Authentication 1** — Web Exploitation
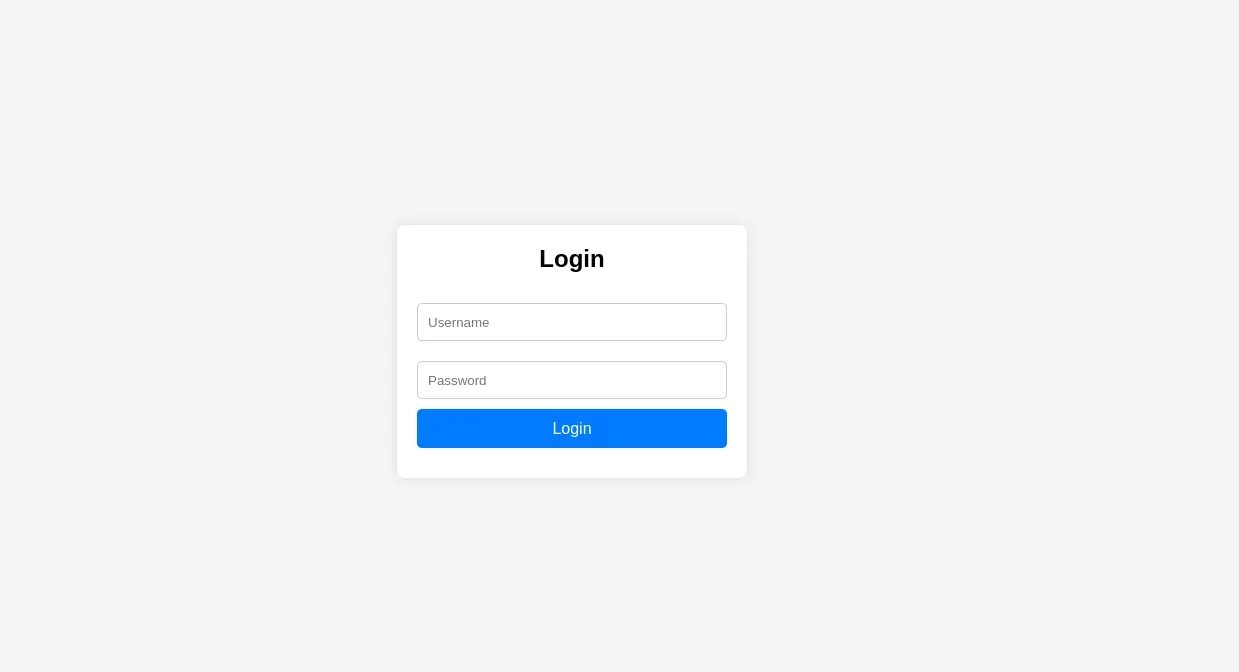
This challenge only provides a website link with no description. From the name of the challenge, it is implying that the security mechanism that validates logins might not be properly implemented.
By checking the source code, we can observe that the login is done via JavaScript and the credentials are stored but encoded in Base64. If we decode the credentials it yields:
**admin** : **akoangadmindito!!!**
Plugging it into the username and password fields we retrieve the flag.

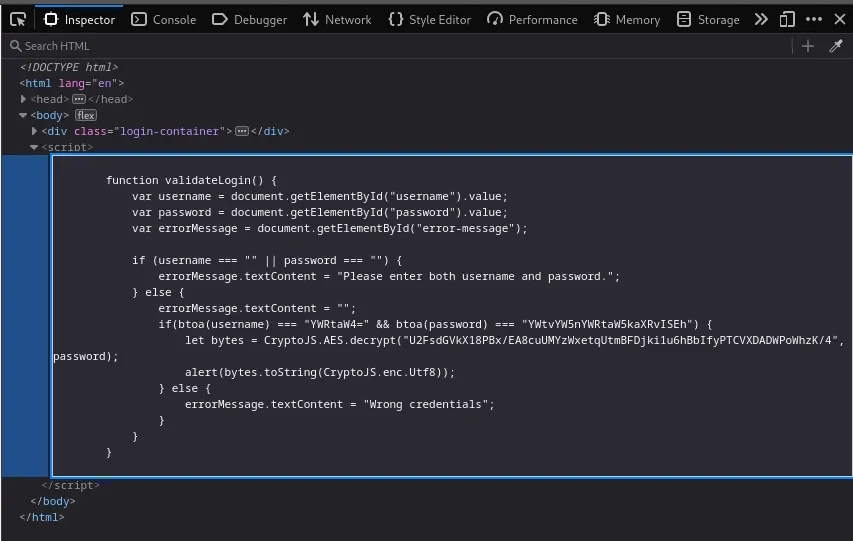
#### **Cicada 1** — Steganography
Based off of the classic Cicada 3301 mystery, the challenge provides an image that is very similar to Cicada 3301’s “recruitment campaign”.
Cicada 3301 used the program **_outguess_** to embed a secret message in their images, however in this challenge a suspicious text appears at the very end of the image. This can be found by using the **_strings_** command.

“tiberius claudius caesar says…” implies that this text may have been ciphered with caesar cipher, an old but very common cipher method. Deciphering it using **_Cyberchef_** yields the flag:

#### **Distress Call** — Misc
_As a ham radio operator monitoring for radio signals, your receiver suddenly detect beeps both long and short that lasted for a few seconds. Can you decode what it is trying to say?_
[other]Morse Code that says sossossos3301[/other]
The long and short beeps refer to morse code! Decode it manually or use software and it will yield: **sossossos3301**
#### **Encodings —** Forensics
We receive a PDF file that contains redacted information about number systems and encoding systems.
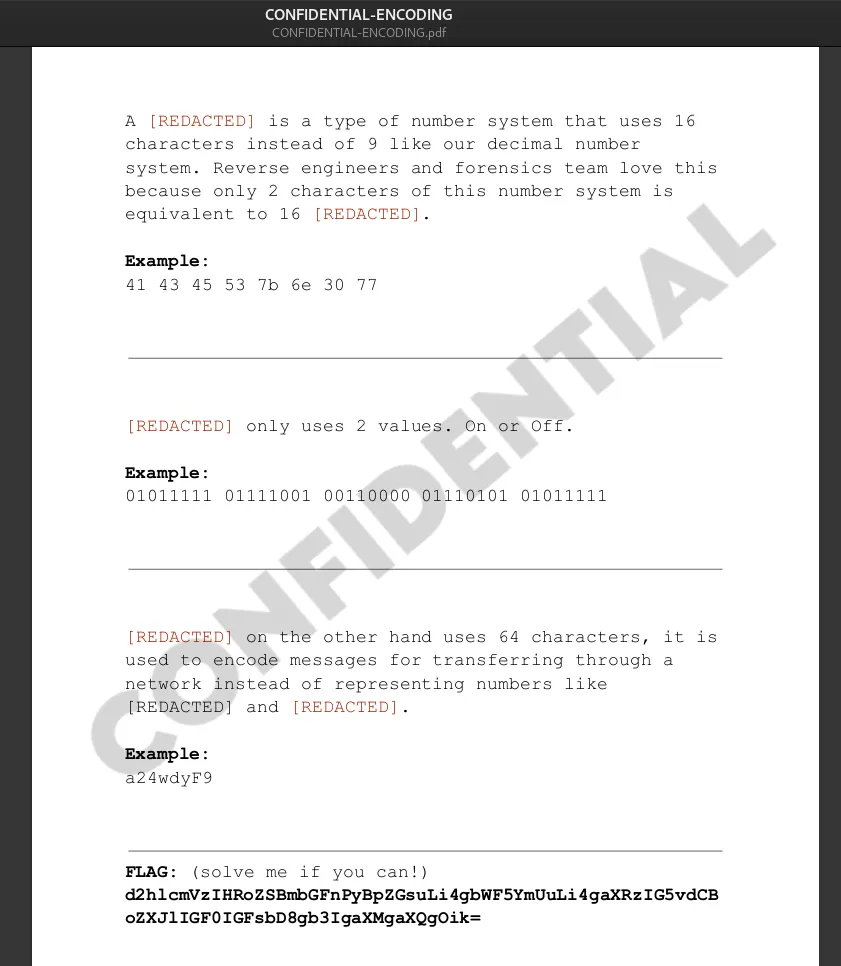
All of the redacted text refer to: hexadecimal, bits, binary, base64, hexadecimal and binary respectively.
You may be tempted to decode the base64 string at the very bottom which claims to be the flag but that only says: _“wheres the flag? idk… maybe… its not here at all? or is it :)”._ Don’t overthink it! The flag is just separated and encoded through each of the examples! Decode each example and retrieve the flag: **ACES{n0w_y0u_kn0w!}**
#### **Fix Me 1 —** Programming
This is a broken code, but it’s only because of misspelled variables and keywords. You can either rewrite it (in another language or the same language)
```
flag = "'~nli5cuvT@D<"
for index, value in emunerate(flaq[::-1]):
if inbex % 2 != 0:
prinl(chr(ord(value)-1), emd="")
esle:
print(chr(orb(vaIue)+5), end="")
print()
```
…or simply fix the mistakes:
```
flag = "'~nli5cuvT@D<"
for index, value in enumerate(flag[::-1]):
if index % 2 != 0:
print(chr(ord(value)-1), end="")
else:
print(chr(ord(value)+5), end="")
# Yields: ACES{th4nks}
print()
```
#### **Fix Me 2 —** Programming
What a mess! Fortunately for us the only errors here are missing “ and ‘ pair, hence it’s on the easy category.
```
#include
#include
;;;;;;;;;;;;;;
#define FLAG_LEN 18
;;;;;;;;;;
void cheese (char * hot, int dog ) { ;;; // jfjdjekekekekekwi
int left = 0, right = dog - 1;// fifiiii WHHEHEHEHEUEH
while (left < right) {;;; ;;;
char temp = hot[left]; ;;; ;;; /* fjfjfjrj */
hot[left] = hot[right];
;;; hot[right] = temp; ;;; ;;; ;;; ;;;
left++; ; ; ;;; ;;; ;;;
;;;; right--;;
}
} ;; /* fjfjdjjrjdjfjf */ ;;;; ;;;
;;;;; ;; ;;; ;;;
int main() { ;;;;;;
;;; char potato [ FLAG_LEN] = "E?AtgOZ4XKoW4c4m:1 ;; ;;;;;; ;
;;;; /* jdjdjeks wifie */ char tomato[FLAG_LEN ]; ;;;
char beef[4-1+1-1+1-1+1-1+1-1+1-1+1-4+4]; ;;; ;;
int len = strlen(potato); ;; //jejek EJEJJAJisisi ;;;
int beef_index = 0, tomato_index = 0;;;; ;;;;;;;
; ;;;; //bdhdjsoaooIAKAKA
for (int i = 0; i < len ; i++) { ;
beef [beef_index++] = potato[i]; ;;;;;
;;; ;;; /* hello */
if (((i + 1)) % 3 == 0) { ;;;;
; beef[beef_index] = '\0;;;
; cheese(beef, beef_index);;;;;;
;;;;; strcpy( tomato + tomato_index, beef);;;;;
tomato_index += beef_index;;
; beef_index = 0;; ;;;;
} ;;;;
}; ;; ; ; /* hello helloooo */
;;;;;; ;;; ;;;;
tomato[tomato_index] = '\0;;
; ; ;;;;;;; ;;;;;;
for(int i = 0; i < FLAG_LEN; i++) { ;
; tomato[i] = (char)(((int)tomato[i] + 0x0a) ^ 0xa); ;;;;
}; ;
; ; ;;;;
; printf("%s", tomato); ;;;; ;;;;;;;;;
; ;;; ;;;;
return 0; ;;;
};;;;;;;; ;;;;
```
I don’t even wanna bother fixing this mess, just find the lines where it has ‘ or “ and fix it (there should only be 3 of them), it’ll yield: **ACES{th4nks_4g41N}**
#### **Free Wifi —** Forensics
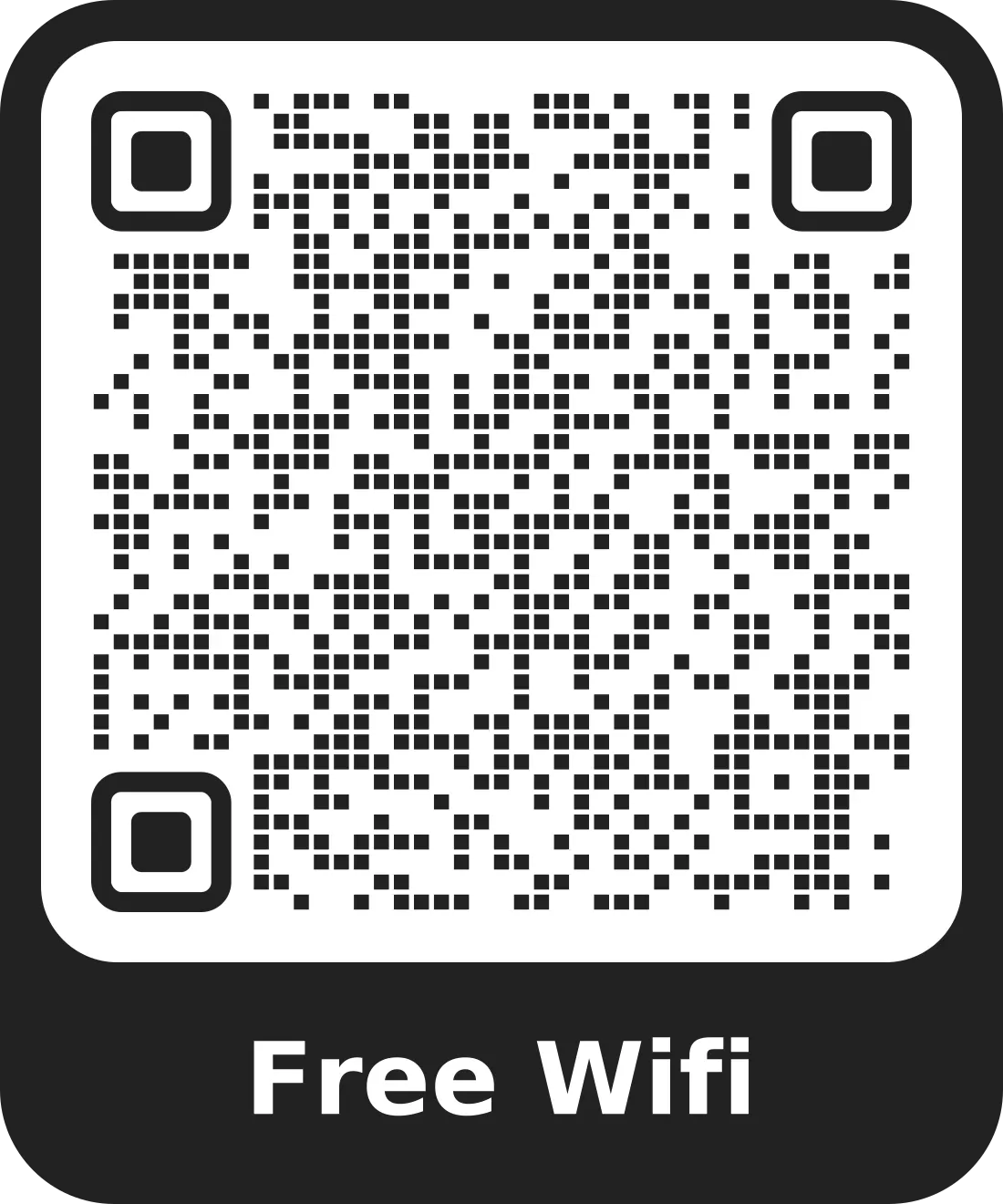
Scan the QR code, it should yield, the flag is in the password field. In Linux, I love using the **_zbarimg_** tool.
```
WIFI:S:Tres Marias Cafe Wifi;T:WPA;P:ACES{p4c0nn3ct_p0};H:false;;
```
#### **Identity —** Forensics
_Who is Kairo?? I bet you didn’t listen to the orientation. If you don’t know, he’s the_ **_Author_** _of this photo!_
REDACTED!
The image was taken in our computer laboratory when we were training for Hack4Gov 3 Regionals. I’m Kairo! The flag is my full name. It can be found in the image metadata! We can use online tools, installed tools or the **_exiftool_** command to view the metadata.
**Kairo** — OSINT
_Kairo? Who is he? I wish you listened earlier at the Orientation…
BTW, his website has the flag, just get it from there!_
The flag is at my website: [https://kairooo.online/](https://kairooo.online/)
It should jump right at you!
### Medium
This challenge uses an original music from Cicada 3301 entitled The Instar Emergence. Although the actual audio used here was a cover by [Mr. h s on YouTube](https://www.youtube.com/@nefariest).
This audio has a distinguishable “chirping” sounds that appear thrice throughout the track. An image is actually etched on the tracks spectogram which is visible through audio editing software like Audacity.
Simply open the audio in **_Audacity_** by importing it. Click on the name of the audio track, on the left, next to the x button, then select Spectogram, below the Waveform. Then it should be visible.
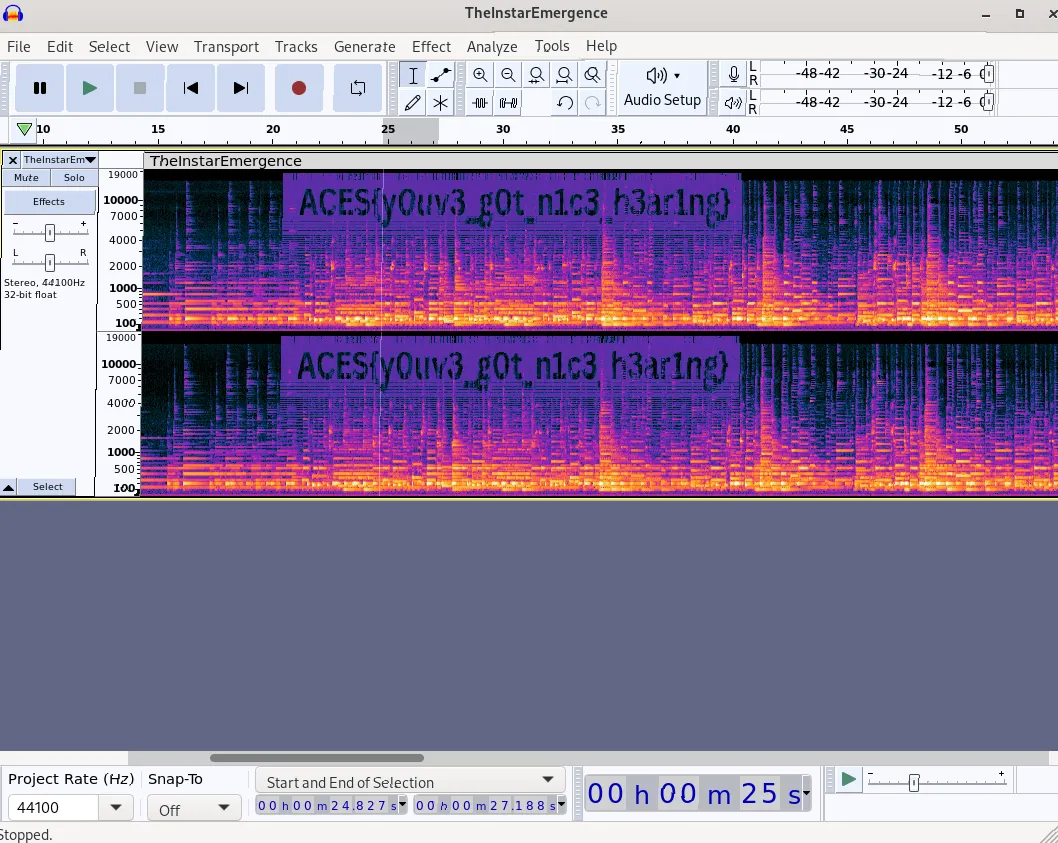
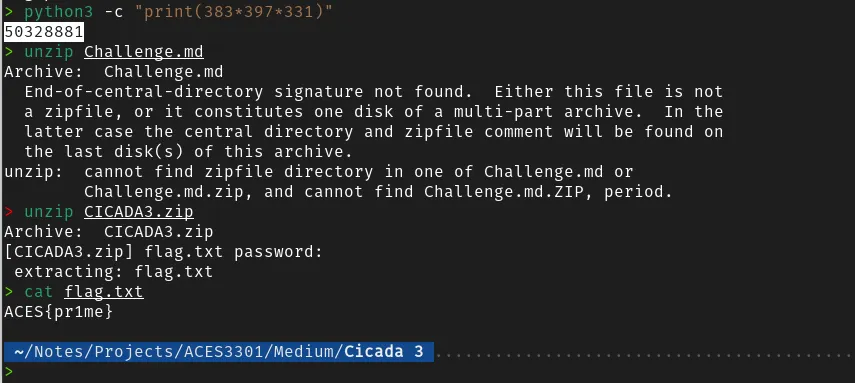
#### **Cicada 3 —** Forensics
Provided with a password encrypted zip file,
_Find three (3) prime numbers with three digits starting with the number 3 associated with the image at the challenge: Cicada 1. Multiply all three numbers and submit it as password in zip file containing the flag._
The three prime numbers are the image width, height and size which are 383, 397 and 331 respectively. Their product, 50328881, is the zip password.
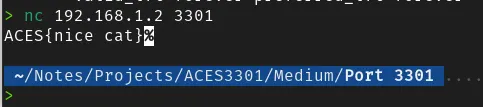
#### **Port 3301 —** Networking
_Something is on 3301! (IP on the whiteboard)_
Some of the participants, visited the IP:PORT as a website, some of them were lucky to obtain the flag, some of them were not, as it was not an HTTP server a TCP server listening for any connections that just returns the flag in return. We simply use **_netcat_** to connect to it!
### Hard
#### **Katipwnan** — Cryptography
_Enclose the odd word out in ACES{…} and submit as flag._
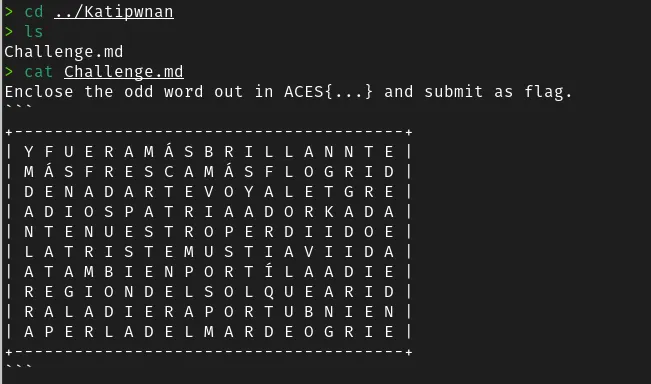
Upon closer inspection of the text, we can see Spanish words. If you researched enough, you will realize that the words are actually in Jose Rizal’s final poem: _Mi Ultimo Adios._ In fact, this is the entire first verse, grouped into 10 lines with 18 characters each, but it’s not arranged in order, it’s jumbled. With the original work as reference, we arrange the lines so that it is in order. The letter K should jump right at you at the thirdmost column from the right, as this letter does not exist in the Spanish alphabet. The only Filipino word, and the only word written vertically: **KAGITINGAN** stands out from the rest of the poem.
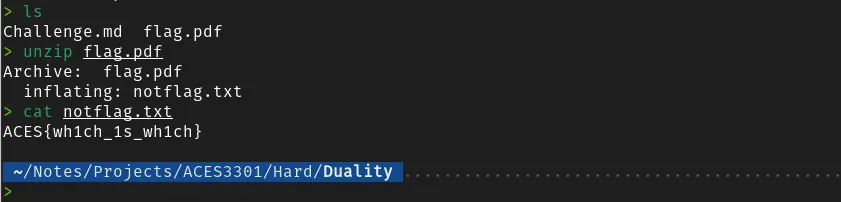
#### **Duality** — Forensics
With the correct tools, this challenge should not be hard at all. This is a hybrid PDF and zip archive. You can simply use the command unzip, or use software to decompress the zip file containing the flag.
#### **Bad Authentication 2** — Web Exploitation
_Get to the admin account!_
Looks like whoever made the Bad Authentication 1 challenge learned his lesson and finally placed the authentication mechanism in the backend where it should be, if we look at the page source there is no more JavaScript validating the login. But did he do it right?
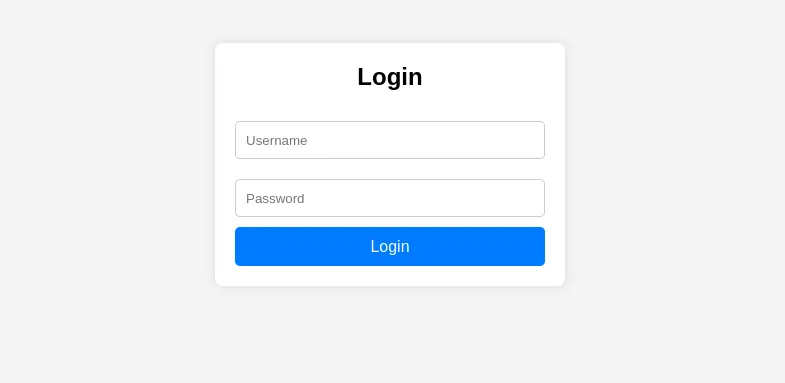
One of the most common security vulnerabilities in login systems is **SQL injection**. They can be easily tested by trying to break the underlying SQL query by passing ‘ or “ characters in the login username or password. If you’re lucky it gives you a detailed error saying you messed up your SQL query, meaning you might be able to manipulate it into telling you the contents of the database, yikes!
This challenge however crashes the website if we try to supply ‘.

Going back to the challenge description, our task is to login as admin, so we try the classic `‘ OR 1=1 —` payload in order to trick the server into saying, hey I’m admin, let me in if my password is correct OR if 1 is equal to 1, which is always true in this case, so the server disregards the password even if it’s correct or not.

This competition really honed my skills, as it gave me my first ever perspective from a challenge creator. The feedback I received from the participants were very positive, and I’m glad they actually enjoyed the challenges. Moreover, the team that I am mentoring, the freshmen Computer Engineering, won this competition solving all of the challenges, 30 minutes before the 3 hour competition was over.
Thank you for reading my writeup! Much love, kairo.